Setting up a new Android phone usually prompts a choice for lock screen security: PIN, password, fingerprint, face unlock, or a pattern lock. Many people choose pattern locks because they’re quick and easy to remember, but that convenience comes with a big security risk, since they are highly vulnerable. The tactile motion leaves traces, screen residue reveals paths, and predictable human behavior makes patterns easy to guess. These factors combined make these locks the weakest link in mobile security.
Pattern Lock Gives You a False Sense of Security
Most people who use pattern lock believe their phone is reasonably protected. It’s not. Compared to other lock options available on Android, the pattern lock is placed at the bottom of the security ladder.
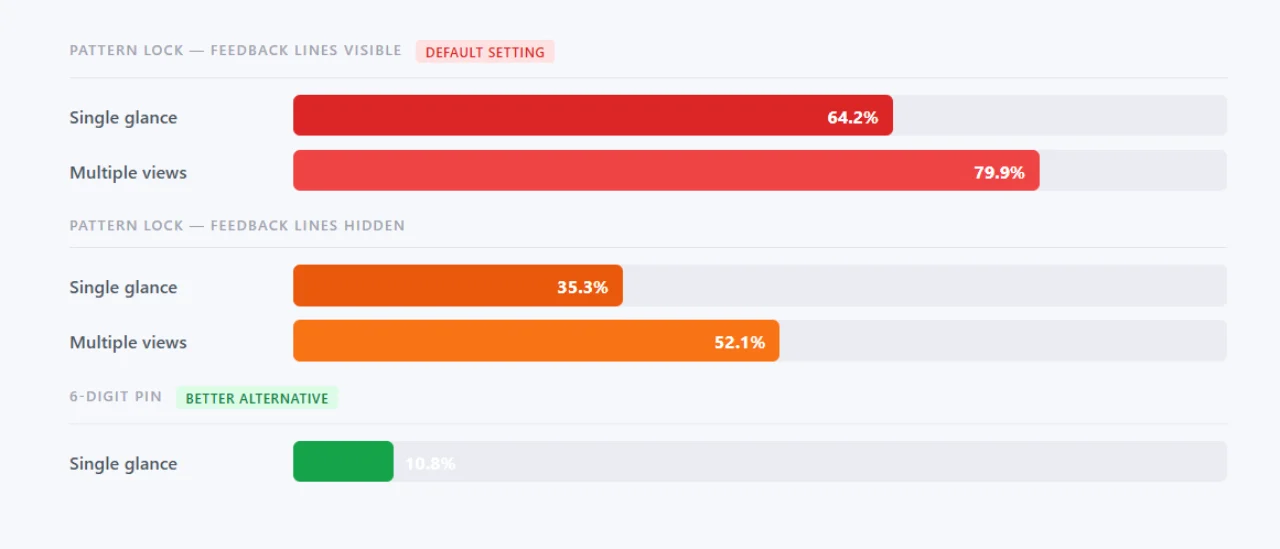
Research published at the Naval Academy and University of Maryland found that shoulder surfers, which refers to when people casually glance at your screen in public, could successfully reproduce a pattern lock 64.2% of the time after a single observation. With just a few looks, the number increases to nearly 80%. By comparison, the same study found that a six-digit PIN was successfully captured only 10.8% of the time from a single shoulder surfing attempt.
According to the research, “We find that 6-digit PINs are the most elusive attacking surface where a single observation leads to just 10.8% successful attacks, improving to 26.5\% with multiple observations. As a comparison, 6-length Android patterns, with one observation, suffered 64.2% attack rate and 79.9% with multiple observations. Removing feedback lines for patterns improves security from 35.3\% and 52.1\% for single and multiple observations, respectively.”
Pattern lock is a visual, gestural input. When you draw a shape or swipe a pattern on your screen, the big arm movements are far easier to observe and memorize than watching someone’s fingertips tap numbers. Even someone sitting across a café who barely pays attention can still remember your unlock pattern.
Researchers Can Crack 95% of Patterns in Five Attempts
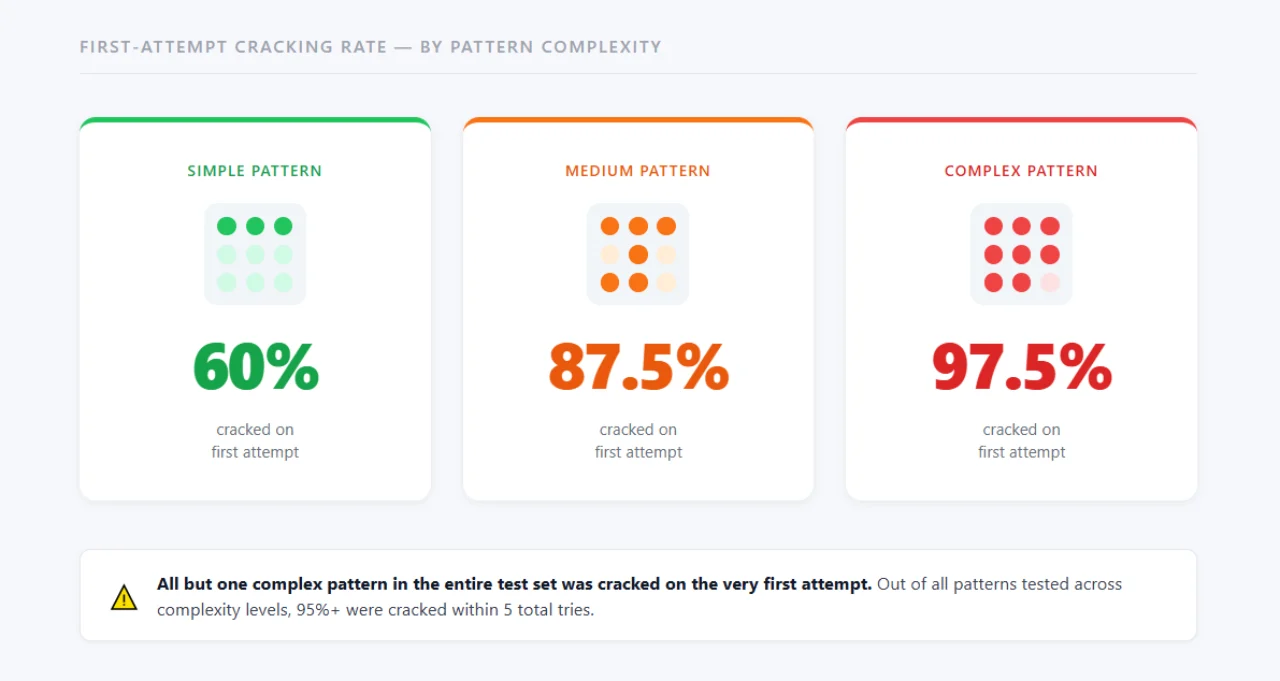
In 2017, a joint research team from Lancaster University, Northwest University in China, and the University of Bath published a study that has become a benchmark in mobile security circles. They developed a video based attack through a standard smartphone camera, and the results were stark:
- Over 95% of patterns were cracked within five attempts.
- 97.5% of complex patterns were cracked in the very first attempt, all but one out of the whole complex pattern test set.
- 87.5% of medium complexity patterns cracked on the first attempt; 60% of simple patterns cracked on the first attempt.
- The attack was successful from up to 2.5 meters away with a phone camera and up to 9 meters using a DSLR.
Complex patterns are easier to crack than simple ones. You think the extra lines and sharp turns add security, but they’re basically a gift to computer vision. A complex shape gives an algorithm more geometric data points to grab onto, which usually lets it identify the exact pattern on the first try. If you keep the pattern simple, the software has to work through more possibilities.
The attack didn’t need to see the screen; it tracked fingertip movement relative to the phone’s position and reconstructed the shape. A nearby person, pretending to scroll through feed on his phone, could film your unlock and have the pattern identified within seconds.
Your Pattern Smudges are a Security Liability
Every time you draw an unlock pattern, you leave an oily trace of your finger on the glass. Under the right lighting — angled sunlight, a lamp, even a phone’s flashlight — these smudges become visible outlines of your pattern.

A University of Pennsylvania study found that smudge attacks successfully identified lock patterns in 68% of cases under favorable lighting conditions and partially recovered them 92% of the time. The researchers only needed a basic camera and angled lighting to capture usable smudge traces.
“To explore the feasibility of smudge attacks against the Android password pattern, our analysis begins by evaluating the conditions under which smudges can be photographically extracted from smartphone touch screen surfaces. We consider a variety of lighting angles and light sources, as well as various camera angles with respect to the orientation of the phone. Our results are extremely encouraging: in one experiment, the pattern was partially identifiable in 92% and fully in 68% of the tested lighting and camera setups. Even in our worst performing experiment, under less than ideal pattern entry conditions, the pattern can be partially extracted in 37% of the setups and fully in 14% of them,” the research stated.
Someone who picks up your phone and tilts it toward a light source doesn’t need any software, algorithm, or technical knowledge. They only look if your pattern is still smudged on the screen, and it often is, since you don’t clean the device every time you unlock it; the route to your data is visible with the naked eye. You could clean your screen regularly, but that won’t happen. You have better things to do than sanitize the gadget fifteen times a day. Some screen protectors make this worse as they catch fingerprints and show every smudge more clearly than a bare screen would.
Humans are Predictably Bad at Creating Patterns
A standard 3×3 Android grid offers 389,112 possible valid combinations (using 4 to 9 nodes). In reality, the actual number of patterns used by the public is much lower because humans are predictable.
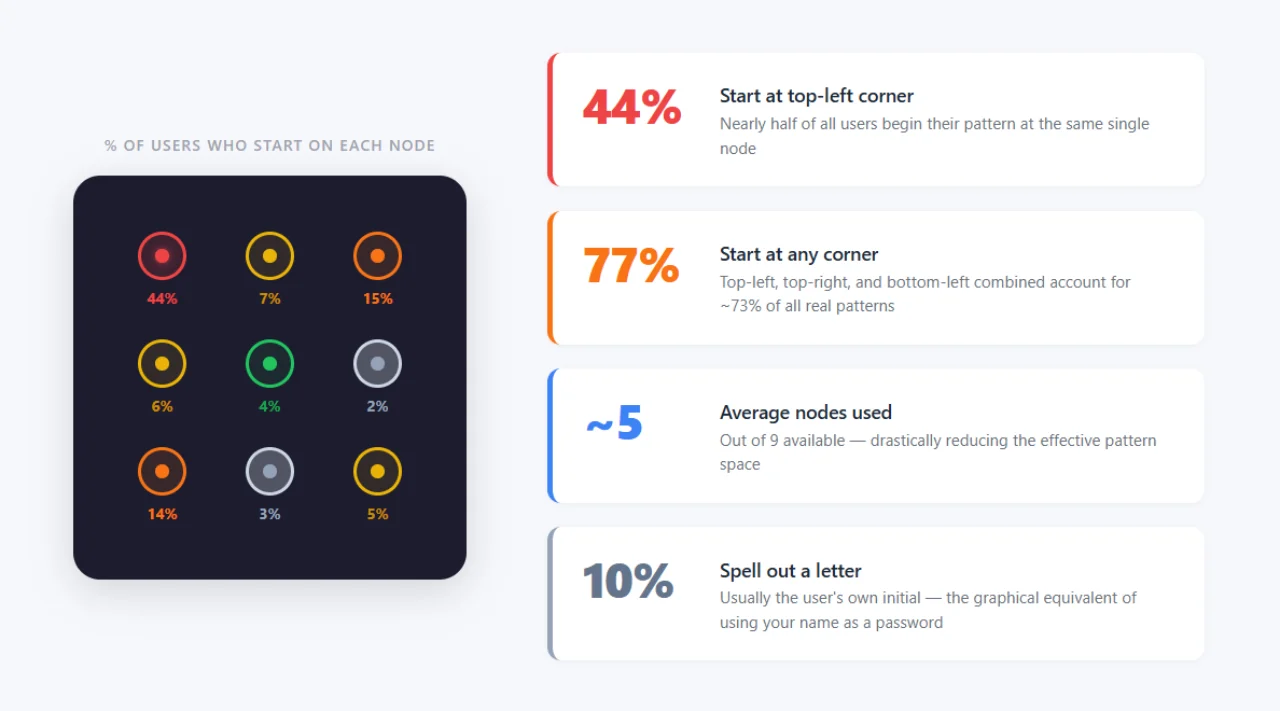
Marte Løge’s research at the Norwegian University of Science and Technology analyzed 4,000 real world patterns and found:
- 77% of users started their pattern from one of the four corners.
- 44% specifically started from the top left corner, and combined with the bottom left and top right corners, it accounts for almost 73% of all patterns people use.
- The average pattern used only 5 of the 9 available nodes.
- Around 10% of patterns spell out a letter, usually the user’s own initial.
Because of these behavioral habits, attackers do not need to guess 389,000 combinations. They can run a dictionary attack based on the most common human shapes and crack the phone in a few attempts. Let’s say someone knows your habits. They know you probably start top left, use five nodes, or likely your pattern will be the first letter of your name. With that, they’ve already crossed out most theoretical combinations without lifting a finger.
Compare that to an Android PIN. You can use up to 16 digits, and that’s 10 quadrillion possible combos at maximum length. Even a basic six-digit PIN provides 1 million possibilities, and most people don’t start their PIN with the top left digit. The same predictability that makes weak passwords like “123456” very common applies to pattern locks. Løge’s research summarized, “people create patterns the same way they create PINs and passwords,” following habits, taking shortcuts, and using personal references.
Pattern Visibility Only Helps the Attacker
Android displays a visible line that connects the dots as you swipe across the grid. This feedback helps you see the shape you draw in real time. But it also broadcasts the pattern to anyone in your vicinity with a clear line of sight.
Research from the Naval Academy study found that shoulder surfers reproduced patterns with visible trace lines 64.2% of the time after a single observation. With multiple views of the same pattern, that number climbs to nearly 80%. Turning off that feedback (via Settings → Security → Make Pattern Visible) drops the single-view success rate to 35.3%, rising to 52.1% with multiple observations. It won’t fix the fundamental problem but only makes the smudge attack and the video based attack slightly harder to execute, while the pattern remains guessable.
Better Alternatives to Secure Your Android Device
Thankfully, Android gives you better options that don’t force you to remember a 20-character password.
- A 6-digit PIN is very secure with a million possible combinations. It requires discrete taps that are easy to conceal from onlookers and leaves overlapping, indecipherable smudges rather than a swipe line. Even a four digits number offers 10,000 options. Unlike patterns, PIN entry involves small, discrete finger taps that are much harder to observe from a distance.
- Want even better protection? Go with an alphanumeric password. Android lets you mix letters, numbers, and symbols to set a password. A random 8-character pass creates about 218 trillion possible combinations. Yes, typing it takes longer, but if you combine it with biometrics, you’ll barely have to type that password anyway.
- Fingerprint unlock is still the king of daily use because it’s fast, doesn’t require visual interaction with the screen that others can observe. Modern Android phones have capacitive and ultrasonic sensors that rarely miss your print. Samsung’s ultrasonic sensors scan actual ridge contours and depth, making spoofing tougher than older optical sensors. The fingerprint remains locked in the phone’s secure enclave and never gets uploaded anywhere.
- Face unlock is more of a mixed bag. If you have an iPhone or one of the few Androids with dedicated infrared depth mapping, it’s secure. However, if your phone uses the standard selfie camera for face ID, it’s a 2D gimmick. A high-resolution photo can mostly fool these versions, so verify if your smartphone performs a 3D scan or simply takes a picture before you rely on it.
For most users, the sweet spot is a fingerprint lock, paired with a strong 6-digit PIN or a password with letters and numbers. Fingerprints are easy, and the PIN backs up if things go sideways with the scanner.