A Linux patch suggests that Intel engineers plan to implement a feature that tags your system as vulnerable if you’re running outdated microcodes, (via Phoronix). This comes in light of the recent Intel 13th Generation and 14th Generation degradation fiasco, which is now pushing Team Blue towards a class action lawsuit.
The patch argues that you cannot run a system with old microcode and consider it safe. Microcode is basically a set of instructions in the CPU that can be updated post-launch to fix critical flaws and security vulnerabilities. The patch proposes that users should be informed clearly and concisely that their PC is potentially unsafe – marking the system as vulnerable or not vulnerable. The author calls to report this vulnerability in “/sys/devices/system/cpu/vulnerabilities/old_microcode“, so that a single file can be used to prompt the user to update their microcode.
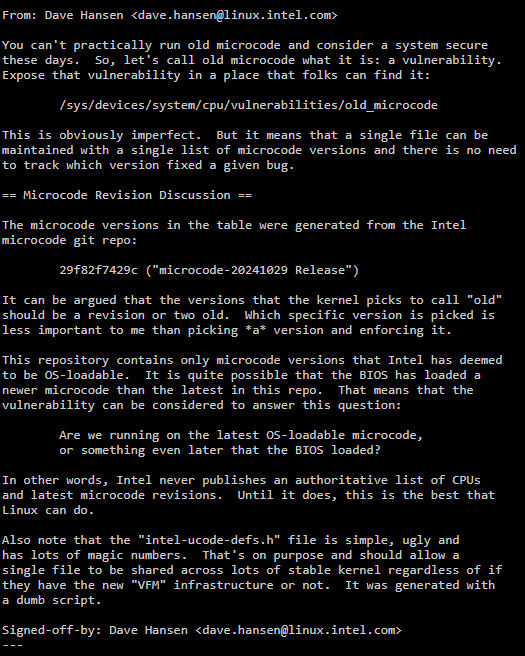
A new X86_BUG_OLD_MICROCODE flag has been introduced which will be used to identify if the CPU is running old microcode. For most CPUs, Linux will maintain a list featuring the latest microcode versions based on Intel’s git repository.
This approach has a slight flaw, since microcodes can be updated through the BIOS or the Operating System’s kernel. The CPU generally chooses the most recent microcode, however, if the BIOS’s microcode is newer, then the system might report a false positive, even though the CPU itself is using the latest release. This is because the aforementioned git repository only hosts OS-loadable microcodes. If a particular BIOS vendor pushes a new microcode (not a part of the git repo), the kernel will not be able to tell if the CPU is on the latest version. To resolve this issue, the author suggests Intel publish an “Authoritative List” of all CPUs alongside their respective microcodes for ease of use and access.
Of course, this will not restrict you from running old microcode. The motive behind this update is to inform the end-user that…
Read full post on Tom’s Hardware
Discover more from Technical Master - Gadgets Reviews, Guides and Gaming News
Subscribe to get the latest posts sent to your email.








